In today's virtual landscape, our data are frequently at threat. ID fraud is a common problem that can severely harm your financial well-being. To reduce this danger, it's vital to safeguard your virtual persona and implement strong measures.
Begin by creating robust passwords for all your profiles and stay away from using the identical password across. Enable two-factor authentication whenever available to add an extra layer of defense.
Remain mindful when providing your details online. Carefully review websites and communications before accessing URLs. Exercise caution when engaging in payments. Use protected platforms and track your statements regularly.
Report any uncommon activity to the relevant institutions. By adopting these guidelines, you can proactively protect your digital persona and reduce the danger of ID fraud.
Wading Through the Labyrinth: Understanding copyright Laws and Their Implications
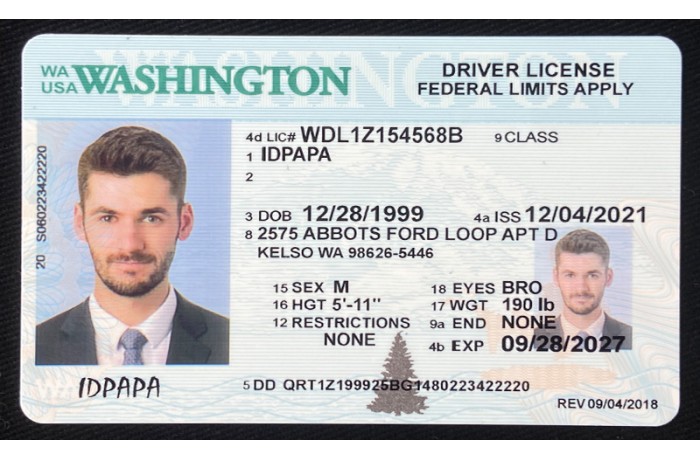
The world of identification can be a complex one, especially when it comes to underage individuals seeking access to establishments that offer alcohol. Fabricating a copyright may seem like an easy way around these restrictions, but the consequences of such actions can be detrimental. Understanding the legal ramifications of possessing or employing a copyright is crucial to avoiding potential legal issues.
- Furthermore, it's important to recognize that regulations regarding copyright vary from state to state, so it's crucial to research the specific rules in your area.
- Possessing a copyright can result in hefty fines, community service, or even incarceration.
- Beyond the legal repercussions, using a copyright can also damage your reputation and make it more difficult to obtain employment in the future.
Biometric Security: The Future of Identity Verification
As technology advances at a rapid pace, so too do the methods used to verify identities. Traditional authentication methods, such as passwords and PINs, are becoming increasingly vulnerable to compromises. Biometric security, which utilizes unique biologicaltraits for verification, is emerging as a more robust and secure solution. This technology leverages features like fingerprints, facial recognition, iris scans, and voice patterns to identify individuals with high accuracy.
- Biometric systems offer enhanced security by eliminating the risk of stolen or shared credentials.
- They provide a convenient and user-friendly experience, as users no longer need to remember complex passwords.
- The increasing adoption of biometrics in smartphones, laptops, and other devices further solidifies its position as the future of identity verification.
While biometric security presents numerous benefits, it also raises concerns about privacy and data protection. Implementing robust safeguards to ensure the preservation of sensitive biometric data is crucial. As we move towards a future where biometrics play a central role in identity management, striking a balance between security and privacy will be paramount.
Moving Past Passwords
In today's digital landscape, the traditional login protocol is increasingly becoming a vulnerable point. Cybersecurity threats are constantly evolving, making it imperative to explore more robust and innovative identity validation technologies. Biometric authentication, leveraging unique biological traits like fingerprints or facial recognition, offers a promising solution by providing a higher level of security than passwords. Additionally, multi-factor authentication (MFA) adds an extra layer of protection by requiring users to provide multiple forms of identification, such as something they know, something they have, and something they are. These advanced technologies aim to create a more secure and seamless user experience, protecting sensitive data and improving online safety.
Leveraging these innovative approaches allows organizations to mitigate the risks associated with traditional passwords and establish a more secure foundation for digital identity.
Addressing Identity Theft: A Multi-Layered Approach
Protecting Ethical ID manufacturing your identity/personal information/data is paramount in today's digital landscape/world/environment. Identity theft, a growing/increasing/rampant threat, can have devastating/severe/profound consequences. Combatting this menace/issue/problem requires a multi-layered approach that encompasses several/various/multiple key strategies/measures/steps.
One crucial layer/aspect/element is strong/robust/comprehensive cybersecurity practices. This includes using complex/unique/strong passwords, enabling two-factor authentication/verification/approval, and being vigilant/aware/careful about phishing attempts/scams/schemes. Regularly monitoring/reviewing/checking your credit reports for any suspicious/unusual/irregular activity is also essential.
Additionally, adopting/implementing/embracing best practices for handling/protecting/safeguarding your personal/sensitive/confidential information can help mitigate/reduce/minimize the risk of theft.
Be mindful/cautious/conscious about sharing details/information/data online and be wary of unsolicited/unknown/suspect requests for credentials/logins/access. Remember, a proactive approach to identity protection is your best defense/weapon/shield against this persistent/growing/common threat.
Safeguarding Your Privacy in a Digitally Connected World
In today's hyper-connected world, privacy is more valuable than ever. As we transmit vast amounts of information online, it's vital to adopt measures to safeguard our digital footprint.
Periodically audit your data permissions on all your devices. Be cautious when interacting with links, and steer clear of questionable websites. Utilize strong, unique passwords for each account, and think about using a encryption software to bolster your online protection.
Keep abreast of the latest data breaches, and train yourself on protective strategies to reduce your risk. Remember, protecting your privacy is an persistent process that requires attentiveness.